Technology
WEBRA 3.0 Technology
March 29, 2006
Principles
In the beginning of our development we had a very clear vision about achievable goals. All around the world there were many software solutions, which promised a lot, but accomplished low customer satisfaction or provided it but the already high-level costs increased further during the implementation phase.
Our principle is to ensure a product and customization for our clients, which provide seamless integration into their business environment, easy-to-use interfaces, high reliability and security to achieve their goals. WEBRA's development principles, methodology and architecture have been designed to fulfill this task.
Independent of the size of your company we ensure "the total freedom of information". This is an effective, not hierarchical, but permissions controlled, user-friendly content publication, intelligent search, workflow follow-up and modification, that is, WEBRA 3.0 architecture.
Main product features
- Content management (Intranet, Internet, Extranet)
- ECM - Enterprise Content Management
- Workflow construction, follow-up, modification
- Application integration
- Document workflow
- Object based architecture
- "Time machine", logging
- SSO- Single Sign On (Active Directory/LDAP integration)
- Cache
- Multi language support
- Scalability
- High availability
System platforms and compatibility
One important benefit of using our WEBRA system is the wide range of compatible systems. WEBRA is suitable for your enterprise system architecture more than any other system. Hence you do not need to purchase additional software licences.
Operating systems: Windows 2003/2008 Server, SUSE Linux, Red Hat Linux, AIX
Web server: Internet Information Server, Apache
Database: MS-SQL, MySQL, ORACLE, PostGreSQL
E-mail server: Exchange, Postfix
High availability
 |
| High availability architecture |
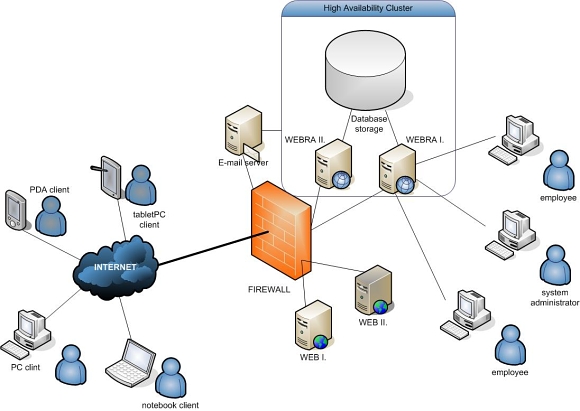
You can set up and run WEBRA on only one server, however if high availability and high loaded service providing via the Internet is the goal, we suggest the architecture on the picture above.
Our reliability for WEBRA software is 99,9% based on 7x24 hours/week schedule. This means just 8,76 hours off during one year.
System tiers: database, business logic, presentation, administrative interface, etc. The separation of the tiers increases the security, ensures more flexibility for later development and provides higher scalability. Business logic tier (WEBRA I:,II.) should be placed on the servers inside the company network, the database tier is worth to be placed on database storage and the secure way for running the presentation tier is on the DMZ zone of the firewall. The separation increases the security of the company network.
Our system can operate on failover and/or load balanced servers to achieve continuous service providing, the first meaning that if one of the servers breaks down, the other immediately takes over the service, and the second is that two or more servers provide the service in parallel.
On the client side you just need a browser for using the portal or the administrative interfaces.
Methodology
We are committed to develop based on standards and software development methodologies. Our company is ISO 9001:2000 approved by the British National Quality Assurance.
During our continuous development an automatic documentation toolkit was born. The quality of our program codes is controlled via automatic modules as well.
A non exhaustive list of our applied standards is as follows:
- UML
- WFMC standards
- Workflow Reference Model
- XPDL 2.0
- Workflow Client Application Programming Interface
- Meta data
- Dublin Core
- W3C
- XML
- XSL
- XHTML 1.0
- WAI-WCAG
- UTF-8
- ISO
WEBRA inside architecture
 |
| Webra system architecture |
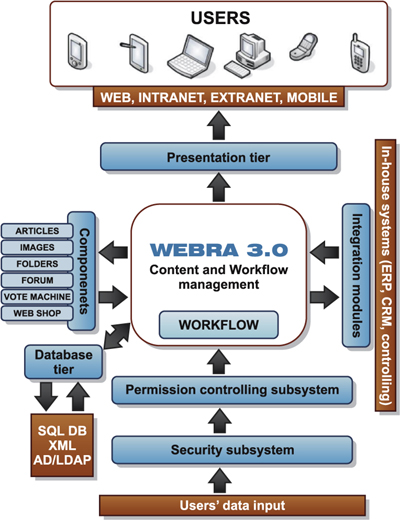
WEBRA ensures seamless integration into your company software environment. It supports the web service integration (for example: SOAP), the XML communication. WEBRA itself is an XML based engine, so it can communicate via simple XML transformations with other systems. The security and permission controlling subsystems take care of authentication, access checking and avoiding security breaches.
The presentation tier transforms the language elements and generates the appropriate output format.
The database tier hides the data sources, so the system can operate with a wide range of databases.
Webra International, LLC. 1087 Budapest Könyves Kálmán krt. 76, Hungary Ph: +36 30 9148 539
